What is Somnium?
Somnium is a Python-based security testing tool designed to validate your network security infrastructure by simulating real-world threat scenarios. It generates controlled malicious traffic to test the prevention and detection capabilities of your firewalls, proxies, IDS/IPS systems, and SIEM solutions.Why use Somnium?
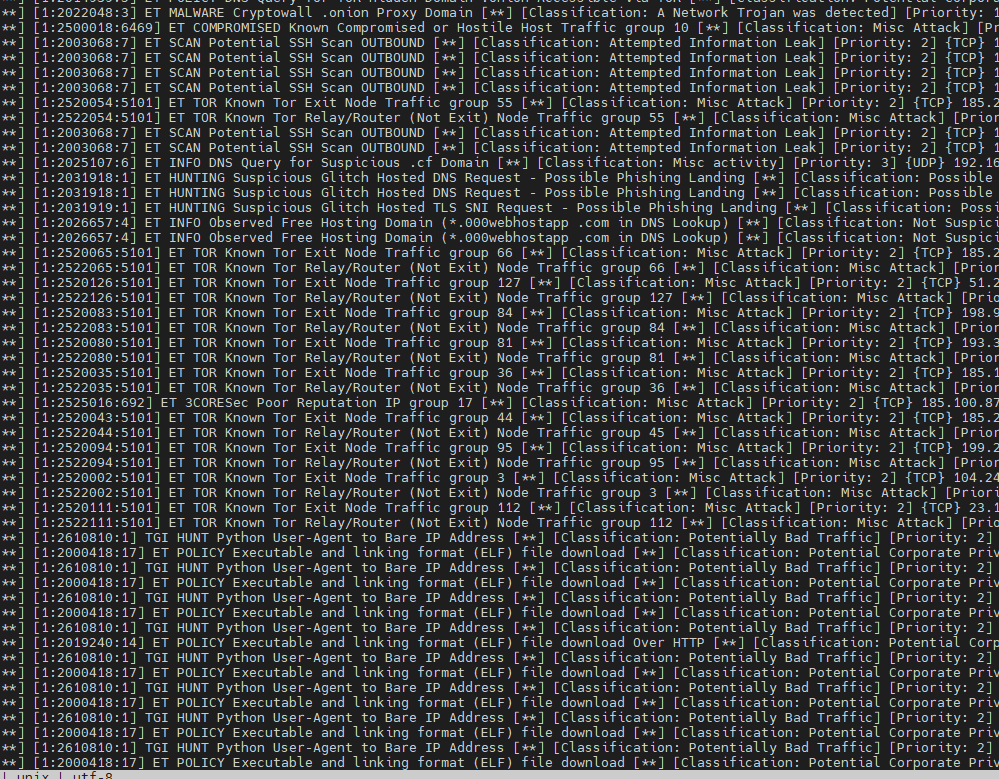
Security teams need to validate their defensive controls work as expected. Somnium provides a safe, controlled way to:- Verify detection rules - Confirm your IDS/IPS signatures detect malicious connections
- Test blocking policies - Ensure your firewall blocks connections to known bad IPs and domains
- Validate SIEM alerts - Generate threat activity to test your monitoring and alerting pipeline
- Audit visibility gaps - Identify blind spots in your security monitoring
- Compliance testing - Document that security controls function as required
Threat scenarios
Somnium tests your defenses against nine different threat categories:Known bad IPs
Tests connection attempts to malicious IPs from Cisco Talos, EmergingThreats, and Mirai botnet lists
Phishing URLs
Attempts connections to active phishing sites from OpenPhish feeds
TOR exit nodes
Tests connections to TOR network exit nodes that may indicate anonymization activity
Malware distribution
Connects to live malware hosting URLs from URLhaus
Cryptomining domains
Tests connections to known cryptocurrency mining domains
DGA domains
Generates Domain Generation Algorithm-style domains to test behavioral detection
Remote desktop tools
Simulates connections to TeamViewer, AnyDesk, and other remote access tools often abused by attackers
Bad user agents
Sends HTTP requests with known malicious user-agent strings from spam bots and malware
DNS over HTTPS
Generates encrypted DNS queries via DoH to test visibility into DNS tunneling
How it works
- Download threat intelligence - Somnium fetches the latest threat feeds from trusted sources
- Select random samples - For each test, random samples are selected to test
- Generate network activity - Connections are attempted to the sampled threats
- Log all results - Every connection attempt is logged with timestamps to local files
- Validate in your tools - Use the timestamps to verify detection in your firewall, IDS, proxy, or SIEM
Somnium only generates outbound connection attempts. It does not download actual malware payloads or compromise your system.
Get started
Installation
Install Python dependencies and set up Somnium
Quickstart
Run your first security test in under 5 minutes
Test scenarios
Detailed guide to all nine threat simulation tests
Threat intelligence sources
Somnium leverages threat feeds from trusted security organizations:- OpenDBL - EmergingThreats and Cisco Talos IP lists
- Security.gives - Mirai botnet IP addresses
- OpenPhish - Live phishing URL feeds
- URLhaus (abuse.ch) - Active malware distribution URLs
- SecOps Institute - TOR exit node listings
- mitchellkrogza - Known bad user-agent database
- Netify - Remote desktop application URLs